Sometimes compression is too good...






So just for additional context:
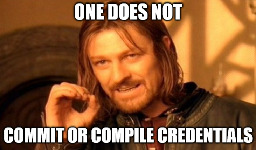
This meme was brought to you by the following API response scheme:
{
"time": "2007-12-24 18:12",
"servertimezone": "Europe/Vienna",
"timezoneoffset": -8
}
when it could have just been
{
"date": "2007-12-24T18:21:00-07:00"
}


As far as I can tell it's the other ways around: IPv4 is getting more costly
Example: AWS started to charge for IPv4 addresses a few months ago - a IPv4 address now costs around $3.6 per month
Well from my personal PoV there are a few problems with that
Well if it's a 32bit timestamp you're screwed after 19 January 2038 (at 03:14:07 UTC)
If you use utc here and a time zone definition changes, you’re boned
I'm pretty sure that things like the tz database exist exactly for such a case.
Just for further clarification, the API works like this:
time is the local (client) time (in this case UTC-7)
servertimezone is the time zone where the server is located
timezoneoffset is the offset of the local time relative to the servertimezone (offset from the servers PoV)
To get the UTC date you have to do something like this:
time.minusHours(timezoneoffset).atZone(servertimezone).toUTC()



I also personally ask myself how a PyPI Admin & Director of Infrastructure can miss out on so many basic coding and security relevant aspects:
On the other hand what went well: